![Updated] Log4Shell: Critical Severity Apache Log4j Remote Code Execution Being Actively Exploited (CVE-2021-44228 & CVE-2021-45046) – Kudelski Security Research Updated] Log4Shell: Critical Severity Apache Log4j Remote Code Execution Being Actively Exploited (CVE-2021-44228 & CVE-2021-45046) – Kudelski Security Research](https://cybermashup.files.wordpress.com/2021/12/screenshot.png?w=840)
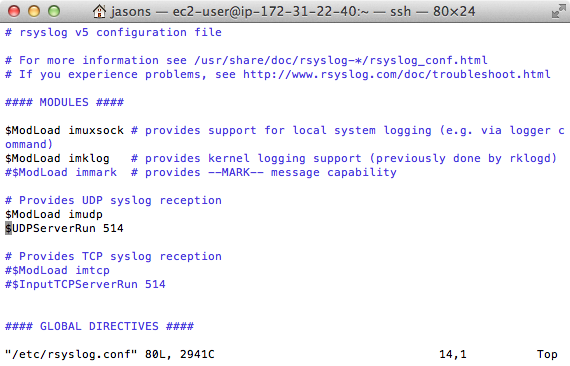
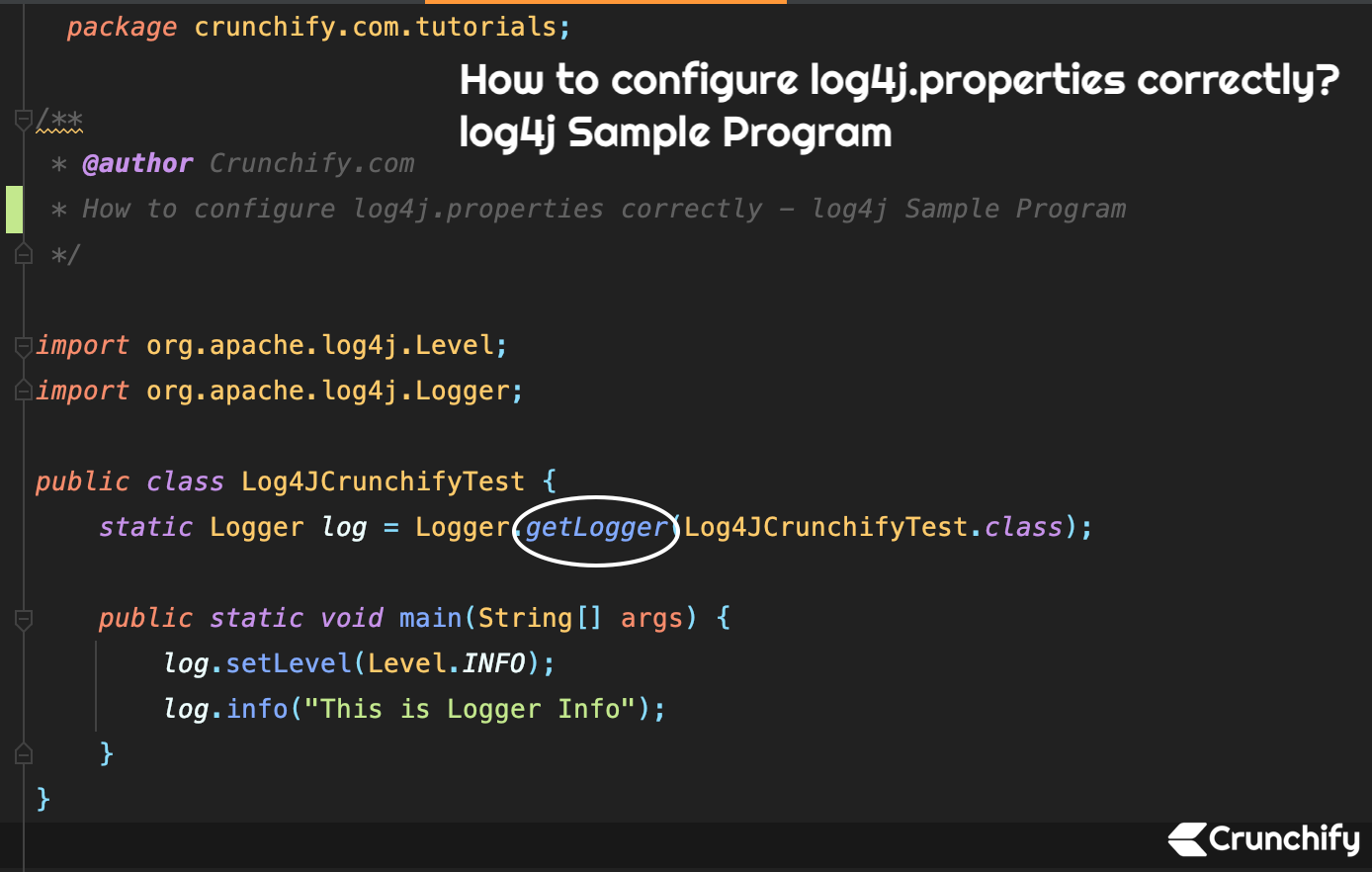
Updated] Log4Shell: Critical Severity Apache Log4j Remote Code Execution Being Actively Exploited (CVE-2021-44228 & CVE-2021-45046) – Kudelski Security Research

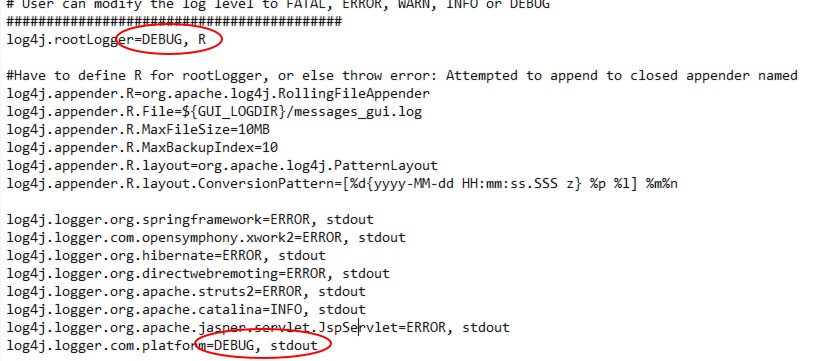
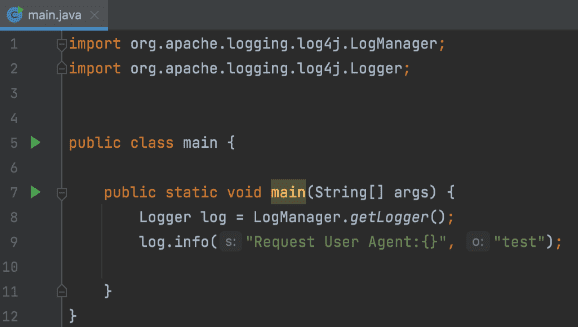
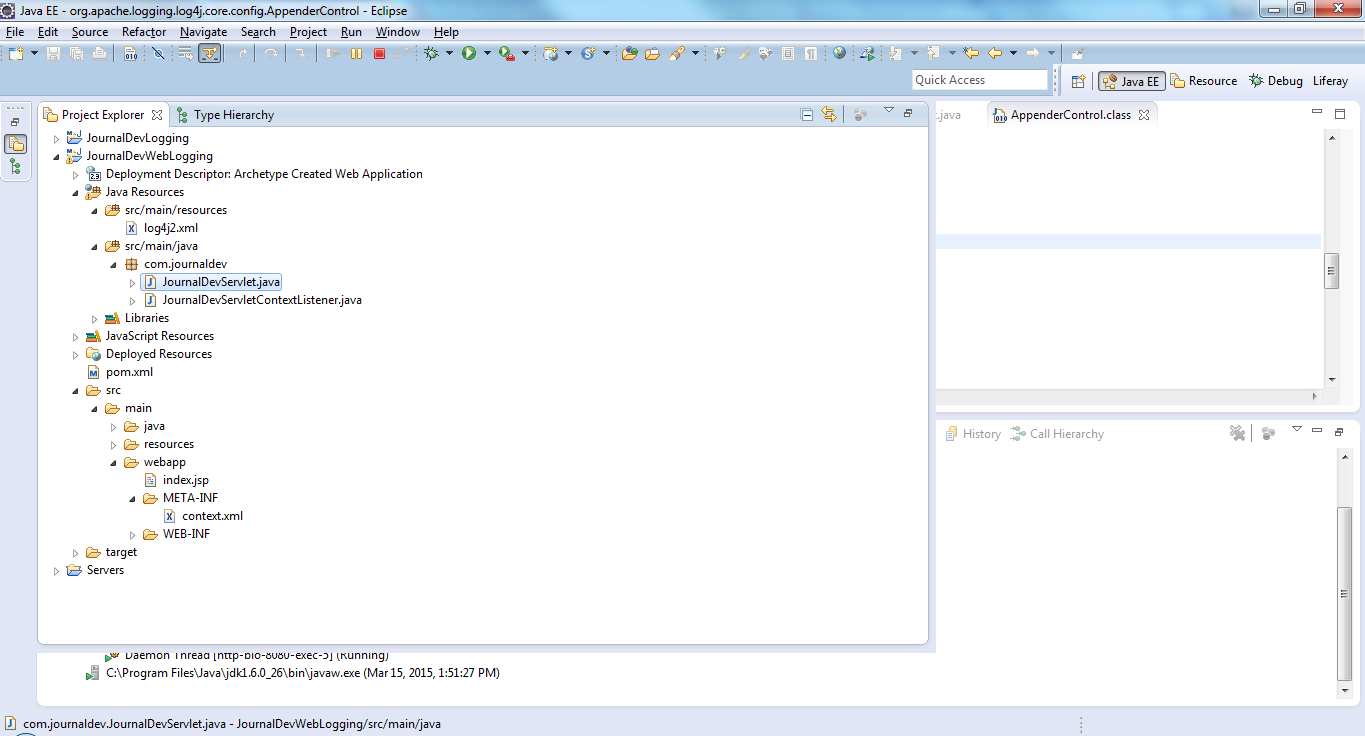
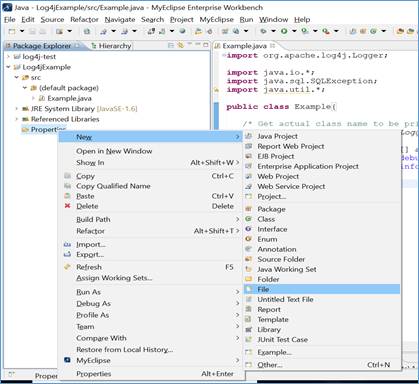
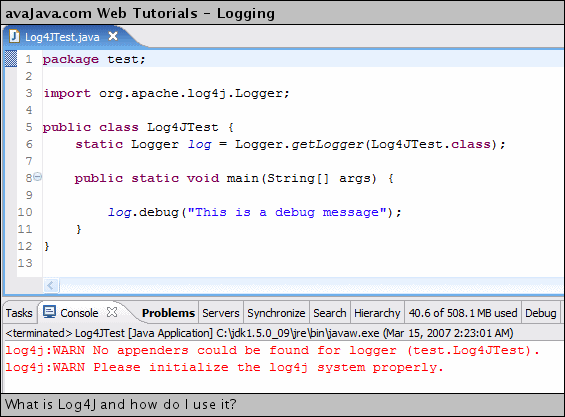
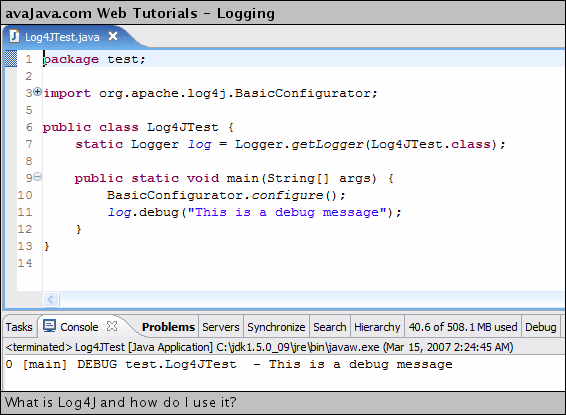
eclipse - unable to run the Log4j2 demo class - While running the class as Java application, Java exception popped out on screen - Stack Overflow

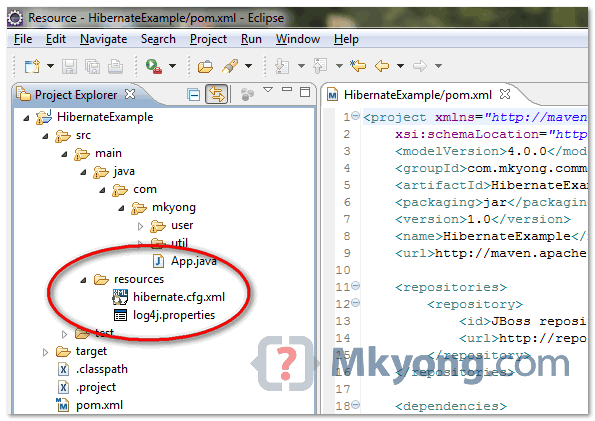
Apache Log4j2 vulnerability fix for Web Service Adapter of SAP NetWeaver Process Integration | SAP Blogs
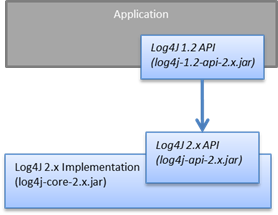
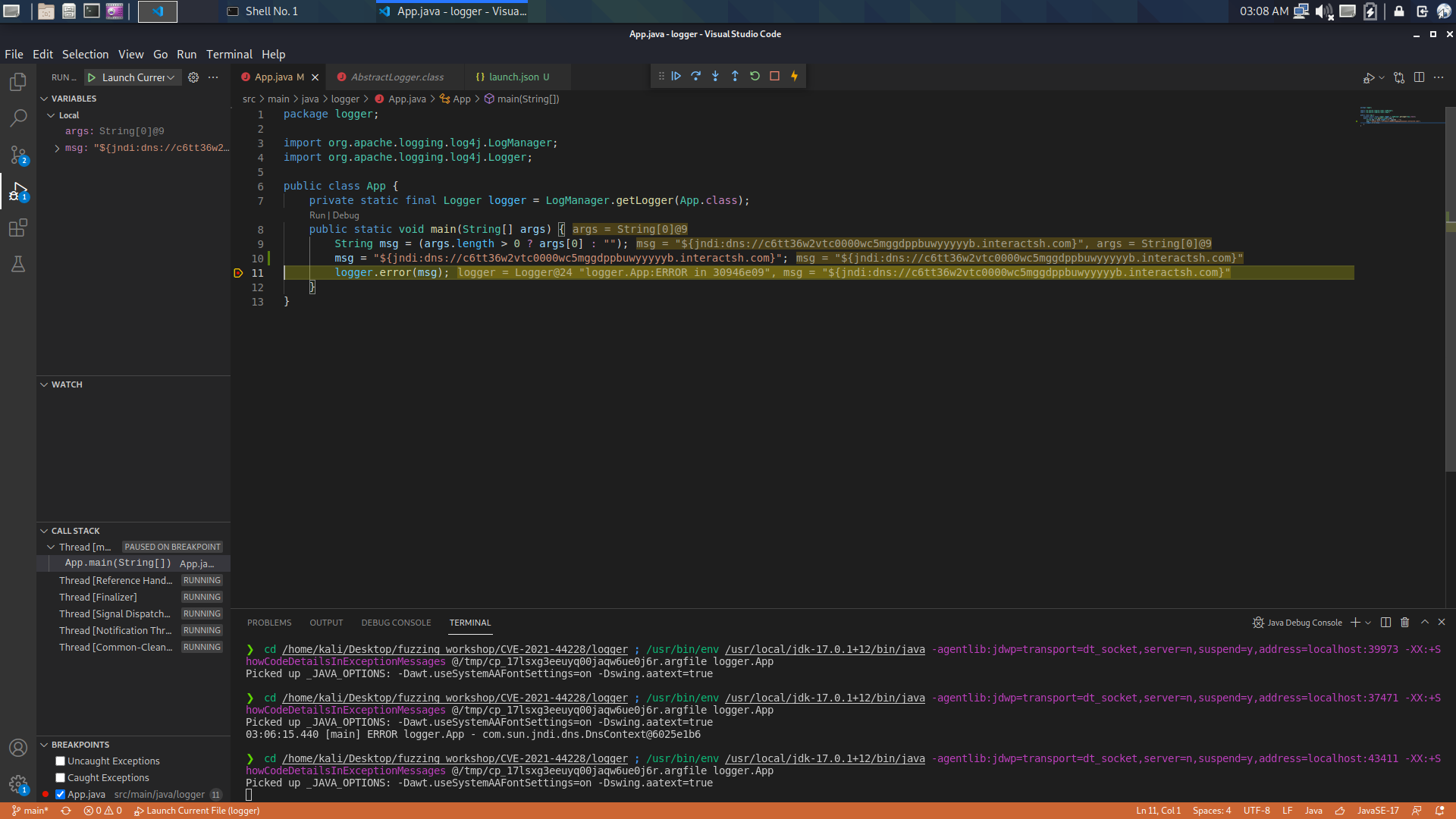
![Updated] Log4Shell: Critical Severity Apache Log4j Remote Code Execution Being Actively Exploited (CVE-2021-44228 & CVE-2021-45046) – Kudelski Security Research Updated] Log4Shell: Critical Severity Apache Log4j Remote Code Execution Being Actively Exploited (CVE-2021-44228 & CVE-2021-45046) – Kudelski Security Research](https://cybermashup.files.wordpress.com/2021/12/screenshot.png?w=1200)