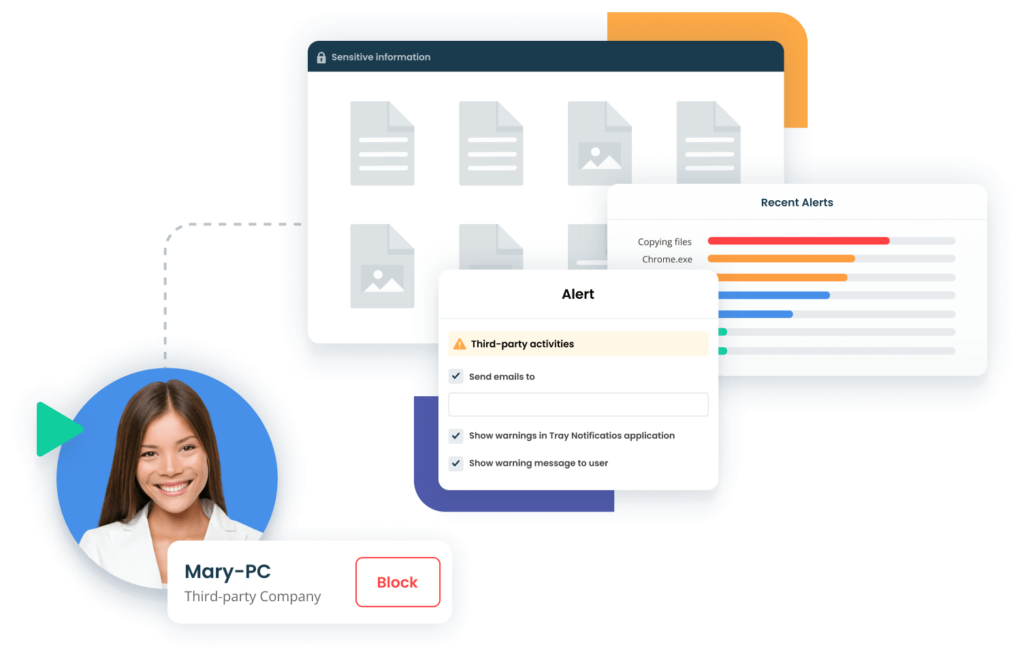
Venminder Announces Venmonitor™, a New Tool to Streamline Third-Party Risk Monitoring Across Multiple Domains
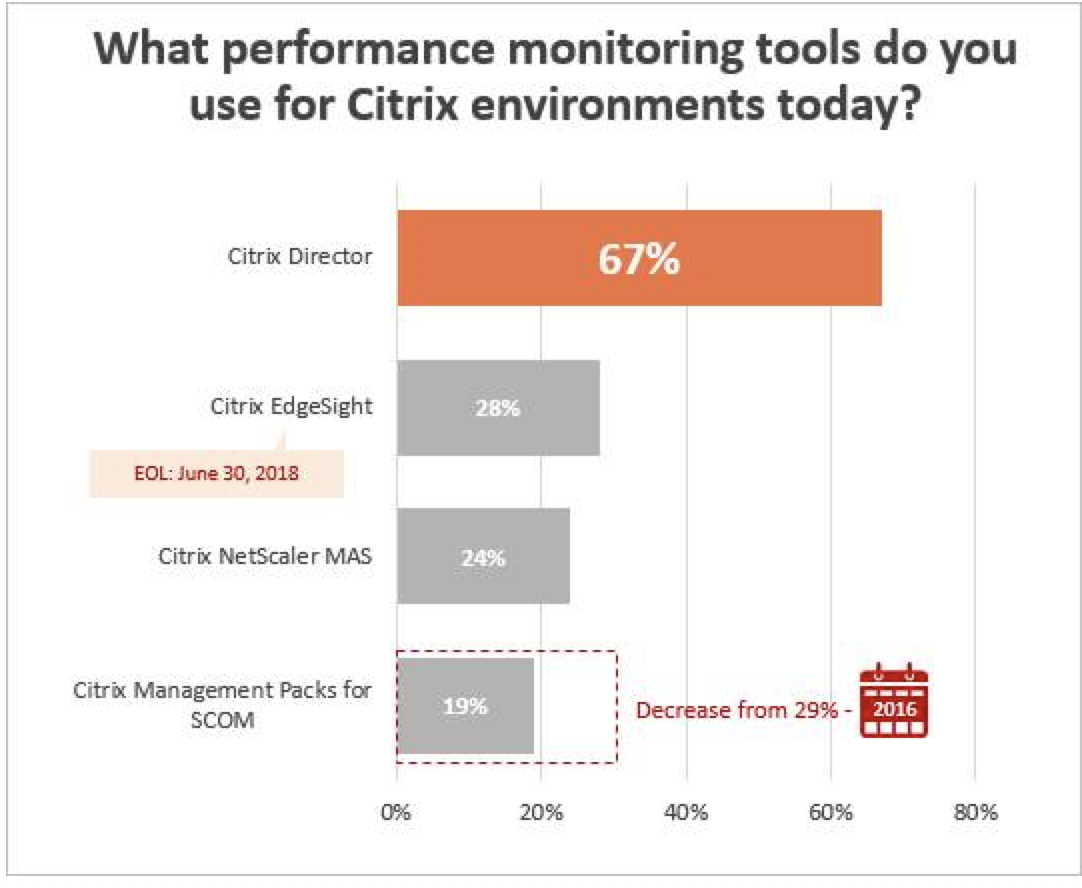
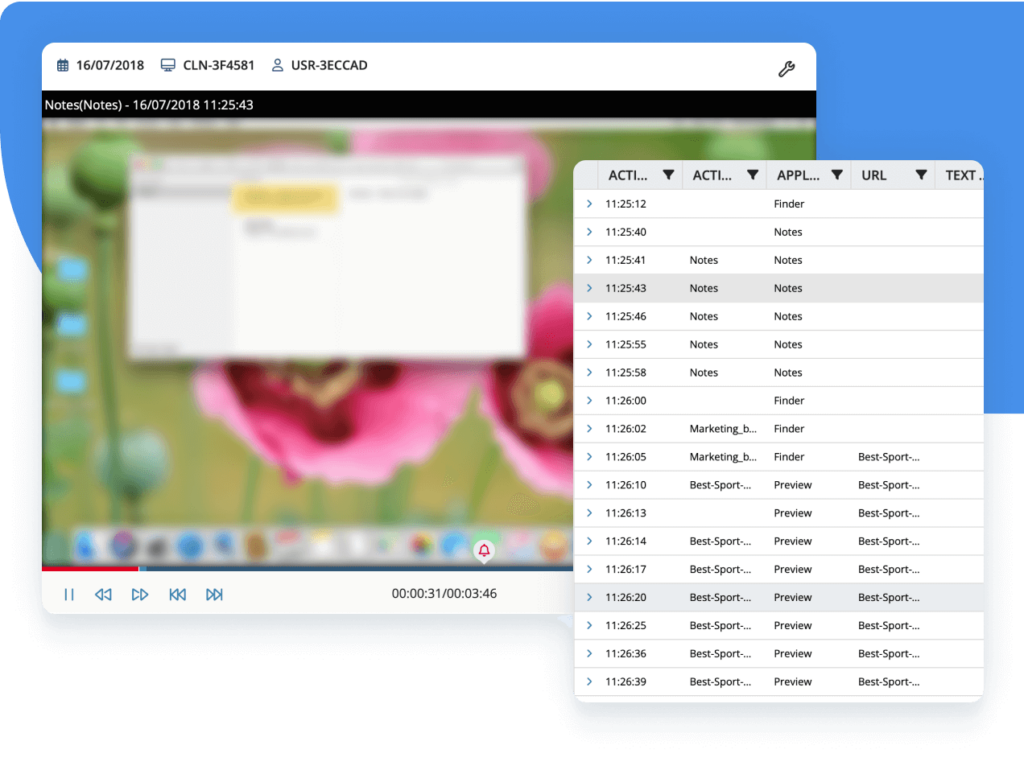
Analyzing and Monitoring the Citrix Digital Workspace: What are My Built-in Options? Why Do I Need Third-Party Monitoring Tools? | christiaanbrinkhoff.com - Sharing Cloud and Virtualization Knowledge

Analyzing and Monitoring the Citrix Digital Workspace: What are My Built-in Options? Why Do I Need Third-Party Monitoring Tools? | christiaanbrinkhoff.com - Sharing Cloud and Virtualization Knowledge


![15 Best IT Infrastructure Monitoring Tools [2023 Comparison] - Sematext 15 Best IT Infrastructure Monitoring Tools [2023 Comparison] - Sematext](https://sematext.com/wp-content/uploads/2021/06/st-infra.png)